Because accessing the Tor network doesn’t take too much time and effort, Mayank Sharma wonders if it’s worth using a Live distro for that purpose. Read our Tails 3.9 Review.
Table of Contents
[sc name=”ad 2″]
Tails (The Amnesic Incognito Live System) is one of the most popular distributions that’s built around the Tor anonymous network. The distro earns its name because of the steps it takes to ensure it pulls a Keyser Soze every time you run it on your computer. There are several other privacy-centric distros that employ Tor. such as Subgraph OS.
The Tails project is very prompt at putting out new releases. It hails the latest v3.9 as its biggest update since it includes two features the team has been hacking away at for over a year. If you’re new to Tails, the distro displays a greeter when you fire it up that enables you to tweak some settings, although this is purely optional and you can choose to use Tails without making any changes.
Besides language and region settings, you can use the greeter to define a password for the administrator user, disable MAC address spoofing which on some computers causes trouble connecting to the internet and change how the distro connects to the Tor network.
As soon as you’ve connected Tails to the Internet, the distro will automatically connect to the Tor network. You can click the Tor icon in the status bar to view the circuits and streams. Once connected you can use the Tor browser and surf anonymously. There’s also the OnionShare anonymous file-sharing program that leverages the Tor network.
Tails 3.9 Review: Privacy, and then some
While you can connect to Tor from your regular distro as well. Tails USP goes the extra mile to protect your privacy as well. For starters it takes special care to not touch the computer’s hard disks, even if it’s got an earmarked swap partition. The distro also uses scripts to wipe your RAM when you shut it down to protect you against any forensic recovery techniques.
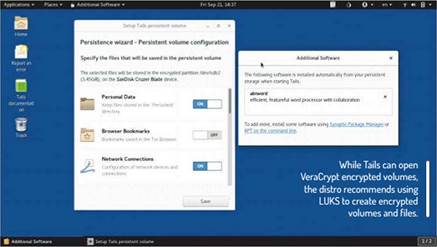
If you boot Tails off a USB drive and use it daily, you can make your life a little easier by creating an encrypted persistent partition. The partition takes over the remaining free space on the USB drive and besides housing files you want across reboots, can also house other settings like network configuration, SSH keys, Pidgin settings, and such. Even if you’ve created a persistent partition. Tails gives you the option to boot into a pristine environment if you don’t need access to your data and settings.
In terms of programs. Tails includes a handful of other security and privacy-centric tools like GtkHash to compute message digests and checksums and KeePassX for managing passwords. There’s also Electrum Bitcoin wallet Nautilus Wipe to securely delete files and MAT for zapping metadata information from files. Beyond its specialisation. Tails includes the usual cocktail of software
you’ll find on many Linux distros, such as LibreOffice, Thunderbird, GIMP, Scribus, Pidgin, Audacity and PiTiVi. It also bundles the Synaptic package manager for fleshing out the distro.
The ease of adding software is one of the two areas of focus of this release. Like any Live distro. Tails will drop any program you’ve installed in the Live environment upon shutdown. With this new release however, as soon as you’ve installed any software. Tails will give you the option to have it installed permanently. If you select this option, the new program will be housed in the persistent partition and will be installed on subsequent boots.
The other major change is the ability to unlock VeraCrypt encrypted volumes. If you’ve got such volumes on the computer, you can use Tails to unlock them from the file manager itself without installing VeraCrypt The Tails developers have pushed this integration upstream into Gnome, which means it’ll be available in other distros that use the Gnome Files and Disks utilities.
Tails 3.9 Review: Verdict
DEVELOPER: The Tails Project
LICENCE: GNU GPL v3
| FEATURES | 8/10 | EASE OF USE | 8/10 |
| PERFORMANCE | 7/10 | DOCUMENTATION | 9/10 |




A cool,Site!