Tails 5.1 Review
Many people don’t like the idea of trusting a third-party VPN provider to keep their online activity private, and instead rely on the open source Tor anonymity network. And no one does Tor better than Tails.
If you’re new to Tails, the distro boots to a welcome tool that you can use to tweak some settings, such as the language and region settings. Furthermore, the screen also rolls in some advanced settings under the + icon, such as the ability to define a password for the default admin user, disabling MAC address spoofing (which could cause connection issues on some computers) and more.
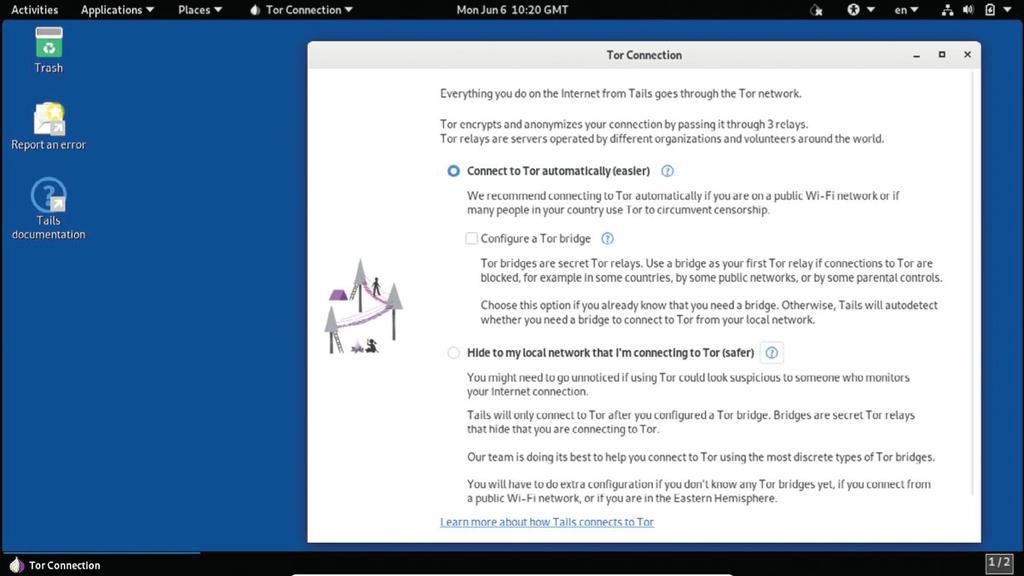
When you’re done with this initial setup and configured your Tails instance, the distro brings up another screen to help you connect to the Tor network. Tails will do all the heavy lifting – all it needs to know from you is how you’d like to connect to the Tor network.
The first option labelled ‘Easier’ is ideal for users who are browsing the web from a public computer or over a public hotspot. You can also optionally toggle the Tor bridge mode if you know that your ISP actively blocks connections to the Tor network. The option is there to save a couple of seconds because Tails will configure a bridge automatically if it can’t connect you without using one, irrespective of whether you’ve toggled the bridge option or not.
The second option labelled ‘Easy’ will take a few more steps to hide the fact that you’re connecting to the Tor network, even from your local network.
Once you complete the setup, Tails will establish a connection to the Tor network and drop you to the Gnome desktop. You can click the Tor icon in the status bar to view the Tor circuits and streams. Once connected you can use the Tor browser and surf anonymously. There’s also the OnionShare anonymous file-sharing application that leverages the Tor network.
Favourable tailwind
Tails is primarily offered as an image for the USB stick, although you can find an ISO image as well. Soon after Tails 5.0 was released, the project asked people to avoid using it because of a security vulnerability in the JavaScript engine of the Tor Browser. Instead, Tails 5.1 released on 5 June became the first official release of the Tails 5.x branch.
Tails 5 is based on Debian 11. While you can connect to Tor from any distro, Tails’ USP is that it goes the extra mile to protect your privacy as well. For instance, it ensures it stays clear of the storage disks on your computer, doesn’t even try to look for a swap partition, and has no option in the file manager to mount the local disks. Moreover, it uses scripts to wipe your RAM when you shut down the distro, to guard you against any forensic recovery techniques.
Regular users of Tails can choose to create an encrypted persistent partition to store files, and settings like network configurations and SSH keys. Tails 5 adds another function to Persistence Storage called Additional Software. This makes it easier for users to configure additional software packages.
Another highlight of the release is the inclusion of the Kleopatra certificate manager and unified crypto GUI. This is borrowed from the KDE project to replace the Easier tools for managing passwords and keys that weren’t actively maintained anymore.
Remember, though, that while Tails does all it can to keep you anonymous on the internet, you’ll have to be equally prudent. Thankfully, the project’s documentation does a good job of educating you on using the internet without leaving a trace.
IN BRIEF
The Amnesic Incognito Live System, popularly known as Tails, is one of the leading distros that’s built to ensure maximum privacy, and anonymity for its users. The Debian-based distro is built around the Tor anonymous network, but also has a few other tricks up its sleeve to protect you as you browse the web.
SPECS
CPU: Any dualcore CPU
Memory: 2GB
HDD: 8GB USB stick
Build: x86-64
VERDICT
DEVELOPER: The Tails Project
WEB: https://tails.boum.org
LICENCE: GNU GPL v3
FEATURES 8/10
PERFORMANCE 7/10
EASE OF USE 8/10
DOCUMENTATION 9/10
Tails is one of those distros that we recommend all road warriors have on a bootable USB stick.
Rating 8/10