Boot-up Security for Windows 10

Soon, the Microsoft operating system will only be able to boot up with a crypto-chip, which checks whether the computer is infected with malware
Windows 10 is more than just a free update that brings back the sorely-missed start menu. The new version is also quite futuristic with regard to things like the system start procedure. In this particular area, Microsoft is strengthening the anti-malware protection by mandating the use of a crypto-chip.
Now, Windows 10 can be installed on random pieces of hardware. However, the following applies to new devices: Each computer that is running Windows 10 must contain a version-2.0 trusted platform module (TPM) within a year. This crypto-chip is necessary for the measured boot procedure.
Microsoft has thus enhanced the hardware requirements for certified Windows devices. When combined with the prescribed ‘secure boot’ procedure, the system will, right at the boot-up phase, be more secure than every previous version of Windows. However, on the flipside, a function for deactivating secure boot is no longer mandatory, but optional. If the secure boot-up facility is active, it can lead to problems with other operating systems that have been installed in parallel, or with the process of using USB sticks or DVDs to boot up the computer.
The fundamental concern associated with measured boot is clear – the process of booting up the device should become more secure. In the case of Windows 10, this applies primarily to the process of booting up smartphones, tablets and computers. Now, tools and functions like virus scanners and firewalls watch over the system when it is in operation, but the boot-up phase is relatively unregulated. If a hacker manages to use a rootkit to subvert the booting routine of Windows, he would gain complete control over the system. In such a scenario, he would be able to hide his software from virus scanners and other protective systems.
Windows 8 had already raised the security level. One milestone was UEFI version 2.3.1 with secure boot. The advantage is that the UEFI firmware cannot be modified by software, and only allows signed bootloaders to be loaded. In the beginning, this represented a problem for Linux, but signed bootloaders are now available for the Linux kernel. With the secure boot procedure, all the components are checked for a valid signature during the boot-up phase. Unsigned – i.e. manipulated – modules are thus blocked before Windows boots up.
No TPM is needed for a secure boot process. If desired, the crypto-chip also secures the boot-up process of Windows 10. Microsoft calls this the ‘measured boot’ process. This new booting routine really does live up to its name, as it takes a multitude of measurements. After the computer has been started, a hash value associated with the UEFI firmware is calculated, and saved in one of the TPM’s 24 platform configuration registers. This involves protected memory areas that cannot be manipulated, and which can only be re-written when the system is booted up again.
According to the specifications, the registers are divided up as follows: Registers 0 through 7 are available for measurements associated with the UEFI firmware, while registers 8 through 15 can be used by Windows itself, e.g. for BitLocker. The remaining registers are available for software produced by other providers, such as virus scanners. The secure boot process is active at the same time, and checks the signatures of the boot components. Before any module is loaded, the measured boot procedure calculates a hash value and stores the result in one of the aforementioned TPM registers.
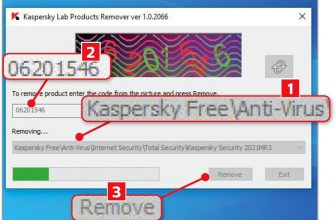
The graphics on the page to the left list the individual steps in detail. After the test associated with the UEFI firmware has been performed, check sums are calculated by the system loader, the kernel modules and the system drivers. These check sums are then saved in the TPM. ELAM (Early Launch AntiMalware) represents a special case – Windows uses this function to allow a virus scanner to jump the gun. Thanks to the ELAM system, a protective programme produced by a third-party provider like Kaspersky, Avira or Symantec can start before the operating system has been loaded. Another hash value is created for such a scenario. The procedure ends as soon as the Windows system boots up and the user can log in. The measured boot procedure then provides an encrypted log file containing a list of all the components that were loaded during the boot-up process.
The highlight of the measured boot procedures is that the log file can be checked afterwards. A function called the ‘remote attestation client’ reads it, and uses the network or the internet to forward it to a test server. The test server runs an analysis to determine whether the loaded components are secure. If they are, you can go ahead and use the computer. If, on the other hand, a module has been manipulated, it is tagged as an infected module, whereupon it should be taken offline.
The advantage of the measured boot process is that an external entity checks whether the activated components are secure. The secure boot procedure does not offer this option, since it runs exclusively on the local PC. However, we are not aware of a corresponding service provider that can be used by private users. Nevertheless, the measured boot procedure is quite important for companies whose employees use their own notebooks and smartphones. Under such circumstances, it must be ensured that the private devices are not infected with malicious software. However, the companies currently have to set up the corresponding test server on their own.