Software you must uninstall NOW

Programs don’t have to be malware to devastate your PC. Jane Hoskyn reveals the software you must remove now – before it turns against you
[sc name=”ad 1″]

Software. Sounds nice, doesn’t it? Soft, sweet and friendly. Not at all like viruses, worms, rootkits and other nefarious creatures of the night that are out to steal your money or secrets or both.
But good software can go bad, often simply because it’s old – it’s a bit like food. Food that’s perfectly delicious and healthy one day can wreak havoc in your tummy the next. Software has use-by dates, too, and if you continue using a program that’s “gone off” your PC won’t thank you for it.
Software – of any vintage – can also acquire dangerous flaws. Certain types of program, notably plug-ins, are especially vulnerable to developing holes that hackers use to funnel malware into your hard drive. Think of ants marching into your larder through a tiny hole in the wall.
Flash is the most timely example of a program that’s got more holes than a rifle range. We know you know Flash is a problem, but it’s only now that companies like Google, Firefox and Amazon are realising it too.
Flash’s near-constant flaws have now reached such a level of urgency, and it’s such a perfect example of a once-great program turning into an unexploded bomb in your PC, that we’ve kicked off our feature with it.
We’ll also cover less familiar software that have become favorite conduits for hackers distributing malware and spyware – it may be happening in your PC right now.
Flash – aargh! Sorry, couldn’t resist. Adobe Flash Player, to give this infernal browser plug-in its full name, has to be patched so often we’re amazed it still exists. If your roof was made out of sticking plasters, you wouldn’t feel terribly confident living underneath it – and Flash is basically a roof made of sticking plasters.
Flash, like other plug-ins, is a small and simple piece of software that hackers can easily embed with malware, and then set the malware to infect your PC automatically as soon as the Flash video or advert plays in your browser.
Many Flash adverts play automatically, so you can see why the plug-in is such a security problem – and instances of this so-called ‘malvertising’ tripled in 2014. Hackers love Flash, and Adobe is really struggling to keep up with the bad guys. Adobe has long since given up releasing Flash security fixes separately, because there are so many of them.
Sometimes we wonder why on earth Adobe – which produces some of the world’s best software, including Lightroom and Photoshop – doesn’t just put this embarrassing plug-in out of its (and our) misery. Many platforms have ditched it already. As long ago as 2010, Apple banned Flash from iPhones and iPads. YouTube dropped it for the safer (and less memory-hungry) HTML5 in January, and Amazon has since banned Flash adverts from its site. Firefox has blocked Flash altogether since July, shortly after the plug-in suffered its third zero-day vulnerability (yes, ‘zero-day’ is as apocalyptic as it sounds).
The consensus seems to be that Flash is a dastardly piece of rubbish that has no place on any sensible person’s computer. You can get it off your PC using Adobe’s own uninstaller (click ‘Download the uninstaller for Flash Player’). If you don’t watch much online video, Flash’s absence won’t make much difference to you, but it will keep your PC safer and may even make it faster.
Flash isn’t all bad. Some of the internet’s most inspiring and exciting sites rely on Flash. For example, We Choose The Moon, an amazing interactive recreation of the Apollo 11 Lunar landing, would be impossible to view if you uninstalled Flash.
There are ways to keep using Flash while minimising its dangers. First, crucially, enable ‘Click to Play’ in your browser (you’ll find this in your settings). Once enabled, Flash is paused by default and only plays when you choose, either by right-clicking or pressing Ctrl+click.
Just before we went to press, Google announced it would pause Flash adverts by default in Chrome from mid-September. You can still play a Flash video, but any “non-central” Flash content will be automatically frozen. This wise move helps to prevent the auto-play malvertising we mentioned above.
If you have a desktop PC and a laptop, you could remove Flash completely from the PC and keep it on the laptop (as long as the laptop runs Windows 7 or later). Make sure to enable ‘Click to Play’ on the laptop.
You must also be meticulous about keeping Flash updated. Download it from Adobe, then double-check you have the latest version.
Flash may be getting all the headlines, but Java – also used to power interactive and animated content – is even more dangerous. This is partly because “updating” Java doesn’t remove old versions from your computer, so your hard drive could contain a disastrous collection of old versions and components that hackers are happily exploiting.
What’s more, Java content (such as games and simulators) tends to absorb your attention for longer than Flash content (mostly brief video clips). That means hackers have more time to attack you. If Flash is like leaving your front door open for half an hour, Java is like leaving it open all day. Given enough time, hackers can easily find a flaw and use it to install malware or, worse, a rootkit that runs constantly and invisibly.
There is a silver lining to all this. Java’s notoriety means it’s fallen out of favor with software makers and users, so the number of attacks has fallen too. In 2013, Java flaws were responsible for a staggering 91 per cent of all computer attacks; that number halved last year – but that’s still rather high.
In the main, Java owes its continued existence to one of the world’s best-loved computer games, Minecraft. Minecraft’s dependence on Java made players vulnerable to zero-day attacks, rootkits and other exploits beloved of Java’s predators.
In March 2015, the game’s developers finally came to their senses and created a standalone version of Java, embedded in a Minecraft launcher that you can download for free. It’s hermetically sealed from your operating system, sandbox-style, to keep you safe from harm. Minecraft no longer requires the standard version of Java, so there’s now no excuse for having it on your machine.
First, disable it in your browser. Find detailed instructions for Chrome, Firefox, Internet Explorer (IE) and Opera here. Then uninstall Java from your PC. You can do this using Windows’ built-in uninstaller, but that won’t get rid of leftover junk files – some of which may be the very files hackers have been exploiting or even installed in the first place. What’s more, there may be numerous versions of Java on your PC, and they all need removing, so a batch-uninstaller such as IObit Uninstaller is more appropriate (see below).
Email program Thunderbird used to be almost as popular as its sister browser Firefox, also made by Mozilla. But while Firefox is holding its own (just) against stiff competition, poor old Thunderbird has been shot down and is full of holes.
Look at Mozilla’s list of security advisories for Thunderbird, and check back regularly if you’re a Thunderbird user. It makes for an alarming read. ‘Arbitrary file overwriting’, ‘Miscellaneous memory safety hazards’, ‘Privilege escalation through Web Notification’ (a flaw that gives any passing hacker more privileges than you) – and all this in only the past few months. Worryingly, some flaws keep reappearing despite regular fixes. Really, is it worth it? We don’t think so. If you use Thunderbird, export any data you want to keep and switch to a new email service.
It’s a sad story. A few years ago, Thunderbird was considered a safer alternative to Microsoft’s Outlook Express, which had more patches than a Victorian quilt. Thunderbird was also faster, more innovative and – quite frankly – cooler. But while Outlook has evolved into a cross-platform tool whose free online version successfully borrows the best elements of Gmail, including seamless integration with online tools such as Office Online and Google Drive, Thunderbird is stuck in the past.
Some antivirus (AV) tools, including the excellent Norton Security have even identified Thunderbird as a Trojan. This is a false-positive – Thunderbird itself is not malicious. However, it’s so full of vulnerabilities that perhaps these over-zealous AVs are wise to block it.
You don’t have to look far online for horror stories about lost iTunes music libraries, disappearing album art and corrupted files. Then there were the problems (teething troubles, if we want to be kind) with iTunes Match and the new Apple Music service.
Over the past year, the Windows version of iTunes has been updated dozens of times in attempts to fix this mess, and to patch security flaws. Meanwhile, Apple claims to take security so “seriously” that it’s quick to lock you out of your account if you forget your password, reset it and then forget what you reset it to. Which, let’s be honest, is easy to do.
Oh, and some Windows 10 users have found that iTunes won’t even recognise their iPhones and iPads.
iTunes cultivated hostility early on by attempting to make itself compulsory. It applied device-based restrictions and ignored the simple drag-and-drop process that made sense to young internet users (for whom drag-and-drop is second nature) and us old-timers (who miss our compilation tapes). Apple took away your control – and it’s now taking away your safety and your music, or at least moving it to somewhere you can’t find it.
Ten years ago, you didn’t have much choice, but now there are loads of free alternatives that work across multiple platforms and let you control your files. We like the simplicity of Foobar2000, which now has versions for Android, iOS, Windows Phone and Windows (PC). It’s free and safe and has a great, supportive website.
If you’re on Android or PC, Google Play Music is a must-have. It’s free and gives you plenty of storage space. It syncs seamlessly between your computer, phone and tablet, lets you edit file info as much as you like, supports playlists and even has a Spotifystyle streaming tool. The iOS version is not as good, but it’s still a decent iTunes alternative.
“Security is our highest priority” said BitTorrent Sync, following a report by researchers (hackers, actually) who revealed the tool’s numerous security vulnerabilities. Sorry, BitTorrent Sync – your priority is not security, it’s file-sharing.
BitTorrent Sync is just one of many ‘client’ programs that let people share data as “torrents”, anonymously and for free, using the BitTorrent platform. Other popular clients include uTorrent and Vuze. None is illegal, and they can be very helpful for sharing enormous files with friends and family, and syncing data between devices.
Less ethically (and more commonly), torrents are used to share copyrighted material for free. If someone gets hold of a preview version of the latest Hollywood blockbuster and distributes it as a torrent, thousands of grateful users will download it for free. If you’re a hacker, you might want to stick a malicious file in there too and sit back as people happily download it.
It gets worse. In August, researchers from City University London explained how a single hacker could launch DDoS (‘distributed denial of service’) attacks by spreading malware via BitTorrent users’ computers, with the aim of shutting down entire servers; banks and news websites are common targets. For a simpler but no less dramatic insight, see DDoS attacks as they happen on the Digital Attack Map.
To avoid becoming a DDoS pawn – and taking a big hit on your bandwidth, and your PC’s health and privacy – get rid of your BitTorrent tools now. Never download any freebie uploaded by an anonymous source without at least running it through malware-checking site VirusTotal.
Windows 10 includes a screen-recording tool, but at the moment it’s pretty basic. For good screen-recording software, you have to pay through the nose, ears and dropped jaw: Camtasia Studio costs £237.
The best free third-party alternative is CamStudio. It’s open-source, easy to use and has decent features, but don’t touch it with a bargepole. Whether it’s actually malicious is debatable – some sites think so (RemoveVirusPC.
com; some think it’s just suspiciously “stubborn” (How To Remove) and others don’t mind it at all (Should I Remove It?).
What’s certain is that its installer is a menace. You might be lucky enough to find it briefly free of PUPs, but we’ve never been able to install it on test computers without coincidentally acquiring a load of adware, notably Binkiland (more about which in a moment).
If CamStudio is on your computer, delete it and its leftover junk using IObit Uninstaller, then run AdwCleaner to weed out any remaining adware and malicious files in your Registry, browsers and hard drive.
As we saw with CamStudio, the reputation-checking site Should I Remove It? can be somewhat generous in its ratings. It even gives Binkiland a ‘green’ (safe) status. The green can only represent the sick feeling we get every time we see it – which is every time we open the browser on our test PC. We delete it, and it comes back. It’s like that permanent damp patch on your bathroom wall.
Binkiland is a browser hijacker, because it embeds itself in your browser (all of your browsers, in fact) and refuses to budge. It’s also likely to be spyware. A similar offender that’s currently doing the rounds is Wajam, which – like Binkiland – claims to be nothing other than a safe search assistant. We’ve already got a search tool, thanks – it’s called Google. We don’t want any others.
Getting rid of these parasites is not easy. First clear them from your browser settings (they’ll be listed under search engines and perhaps also extensions); search for them in IObit Uninstaller and run the force-removal tool; clear leftovers using AdwCleaner; run CCleaner and Malwarebytes Anti-Malware Free, and then do a full antivirus scan.
However, because tools like Binkiland use files that regenerate when deleted, they may still come back. So you should also try the manual file-removal steps outlined for different versions of Windows on the Spyware Techie site.
It recommends checking if hijackers DealKeeper, Optimizer Pro and RegClean Pro are on your hard drive too, and offers removal guides for each one.
You know you’re in trouble when you type the name of a program – in this case ‘My PC Backup’ – into Google and get a ‘card’ at the top telling you how to remove it. The card links to a page on the MalwareTips blog, which claims this adware comes bundled in Cnet installers, installs itself without your permission and then demands cash to back up vital PC files. Shockingly, the program has even been found pre-installed on new laptops.
Symantec’s Norton Security tool can’t remove it, but we did find a detailed manual removal guide on the Lavasoft site. Free video software – with the noble exceptions of VLC and MediaPortal – is not to be trusted. Sorry for the generalization, but it’s based on bitter experience of adware-riddled installers. Even VLC unnerved us when it launched, because it seemed too good be true (it’s not – it’s brilliant, free and safe).
Our occasional ‘Named & Shamed’ columns are like a police line-up of video nasties, including Freemake Video Converter and Free YouTube Downloader – both of which install Wajam. Some sites regard Free YouTube Downloader itself as malware, and there’s a detailed removal guide on the Malware Killers site.
Also beware of DVDVideoSoft, maker of various free YouTube downloaders, screen recorders and BitTorrent clients.
Its installers contain toolbars and browser hijackers that may be on your PC without your knowledge. Look carefully through your IObit Uninstaller list and blitz them using the multi-weapon approach described.
Three cheers to IObit for removing the PUPs that used to plague this program’s setup wizard. It’s now our top choice for uninstalling multiple programs, force-removing programs and plug-ins that just refuse to budge, and automatically cleaning out any leftovers. It integrates with your built-in Windows uninstaller, too.
The free version is our favourite portable tool for quick uninstall jobs. Keep it on a USB stick for getting rubbish off XP and Vista PCs.
This new kid on the block has a ‘Simulate uninstallation’ option that lets you test how a program’s removal would affect your PC before you go through with it.
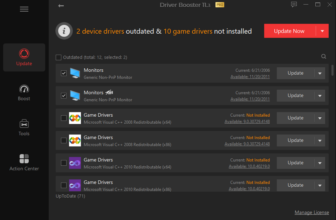
Free online tool that lets you update all your installed programs and plug-ins in one go. The new downloadable Ninite Updater (https://ninite.com/updater) automatically updates all your installed tools – well worth $9.
99 (£6.53) a year.
After you’ve removed any program, even with a powerful tool like IObit Uninstaller, always run AdwCleaner to find and remove malicious leftovers in your Registry, browsers and hard drive.